Zero Trust for the Cloud-Edge Era
Zero Trust and federation are reshaping Europe’s cloud-edge security, enabling verifiable, sovereign collaboration across ecosystems, as outlined by Prof. Norbert Pohlmann from the eco Association and Daniel Theis from the Institute for Internet Security.

©JTKPHOTOz | istockphoto.com
Why federated digital ecosystems are becoming essential for Europe’s data infrastructure
Imagine a Tier-3 data center in Frankfurt. Redundant power feeds, chilled-water cooling, designed for high availability and resilience. By every traditional measure, a fortress. Yet one morning, a connected logistics partner – operating legitimately under a long-standing agreement – issues an automated query that propagates far beyond its intended scope. No perimeter was breached. No firewall was defeated. Trust was simply assumed where it should have been verified.
This is not an edge case. It reflects the defining security challenge of modern digital ecosystems – and it will intensify as Europe’s cloud-edge continuum matures.
The new reality of digital collaboration
Today, digital collaboration is highly relevant to European economic success. Organizations no longer work alone; they build value in dynamic networks across borders and industries. Data moves constantly between cloud platforms, factory floors, and mobile devices. This new reality demands a new approach to how security and trust are handled in fragmented, self-determined ecosystems.
Traditional security models rely on fixed boundaries and assume that trust begins once access is granted. Everything inside is considered secure, while everything outside is considered a threat. When trust is tied to a boundary, organizations risk losing control over systems, applications, and data.
To overcome such silos and build collaborative ecosystems, two concepts are emerging as foundational: federation and Zero Trust. Federation connects without taking control. It provides a framework of shared rules that allows different systems to interact, while each participant retains its data and autonomy. Cooperation is based on shared principles, not on uniform technology, and access is shared without transferring ownership.
Zero Trust complements this model by ensuring that every interaction is verified. It follows one simply rule: “Never trust, always verify.” Every request to access data is checked in real time, regardless of who initiates it or where it originates. Identity, purpose, and context determine whether access is granted.
The business impact is direct. Organizations can onboard new partners in days rather than months, collaborate globally without being locked into a single provider, keep sensitive information at its source while still putting it to work, and secure operations where they happen – on the machine, in the vehicle, or at the hospital.
The end of the perimeter
Traditional security models were built on the idea of a clear boundary. Once users or systems passed that boundary, they were considered trustworthy. This approach worked in stable, centralized environments.
That environment no longer reflects reality.
Organizations now operate across multiple cloud providers, distributed infrastructures, and cross-company networks. Users connect from different locations and devices. Machines and services interact automatically across organizational boundaries. Data moves continuously between cloud, edge, and on-premises systems.
In this setting, the distinction between “inside” and “outside” disappears. When trust is tied to location, a single failure can expose large parts of the system. Long-standing permissions no longer reflect changing conditions. Security becomes fragile instead of resilient. Trust must therefore be established at every interaction – not assumed.
Federation: connecting without centralizing
Federation provides the structural model for this new reality. It allows independent organizations to collaborate without being forced into a single system or controlled by a central authority.
Each participant retains control over its own IT environment, data, and rules, while cooperating based on shared principles and interoperable identity systems. In a federated setup, access replaces transfer. Cooperation works because all participants follow the same principles, not because they use the same technology.
Federation creates what can be described as a “system of systems.” Diverse IT environments are connected through defined interaction points rather than standardized into one platform.
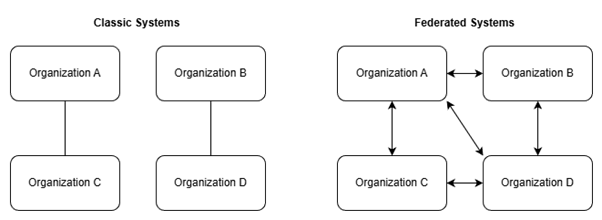
Figure 1: Classic vs. Federated Systems
This avoids dependency, reduces lock-in risks, and allows ecosystems to grow organically. For Europe, digital collaboration must reflect a diverse industrial landscape while preserving sovereignty and openness.
Zero Trust: from concept to operating principle
Zero Trust starts with a simple assumption: no interaction is trusted by default. Every request must justify itself. Verification becomes continuous, with systems evaluating who is requesting access, what they intend to do, and under which conditions.
Being “inside the network” offers no special privilege. Trust becomes an ongoing process rather than a fixed state.
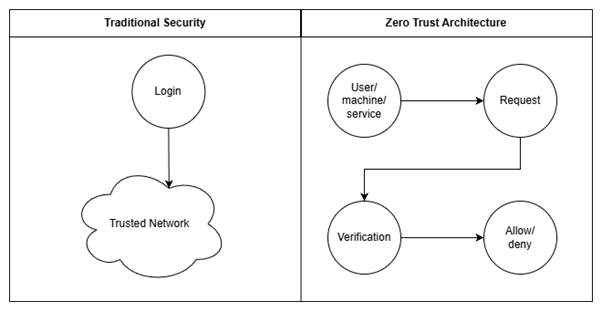
Figure 2: Traditional Security vs. Zero Trust architecture
This changes how organizations operate. Responsibility remains local. Each organization decides when and how others may access its systems and data.
In distributed ecosystems, trust must be constructed from verifiable elements. Identity confirms who is making a request. Policies define the conditions for access. Permissions are limited to specific purposes and timeframes, and trust is continuously reassessed. Trust no longer resides in infrastructure – it travels with each interaction. This enables a crucial balance between data sovereignty and interoperability.
The cloud-edge reality
Data is increasingly created and processed close to where events occur – on factory floors, in vehicles, and in healthcare systems. Organizations operate across cloud, on-premises, and edge environments simultaneously. These environments are dynamic, decentralized, and often time-critical.
A static trust model cannot keep up with this complexity. Zero Trust enables decisions to be made locally while following consistent principles across the ecosystem. For data centers, this represents a strategic evolution: they remain essential, but as part of a distributed architecture where trust – not just compute – becomes a core capability.
From principle to practice
The FACIS project, part of the European 8ra initiative, demonstrates how these concepts empower digital collaboration and how they could be implemented in practice. FACIS shows how independent organizations can collaborate securely within a digital ecosystem without surrendering control over their data or systems.
It provides governance models, onboarding mechanisms, and trust architectures that could operate under real-world conditions. The XFSC open-source tool stack supports this approach by enabling verifiable identities, policy-based access decisions, and trusted interactions across organizational boundaries. Zero Trust is not added as a separate layer: it is embedded across the entire system.
A strategic imperative for Europe
Federation and Zero Trust align with European initiatives such as Gaia-X and eIDAS 2.0, as well as with international frameworks including NIST SP 800-207. Together, they support a model of digital collaboration that is open, sovereign, and interoperable.
The competitive question is changing. It is no longer only about infrastructure scale, but about the ability to collaborate securely without central control and to make trust verifiable by design.
Zero Trust and federation are leadership choices, not just IT projects. They determine how organizations collaborate, protect intellectual property, and scale in a distributed digital economy. Trust should not be left to chance. It must be designed into strategy, architecture, and operations from the outset.
This article is based on the white paper: “Zero Trust in Federated Cloud-Edge Ecosystems” by Daniel Theis and Prof. Dr. Norbert Pohlmann (commissioned by FACIS)
📚 Citation:
Theis, Daniel, & Pohlmann, Norbert. (April 2026). Zero Trust for the Cloud-Edge Era. dotmagazine. https://www.dotmagazine.online/issues/data-centers-digital-infrastructure/zero-trust-for-the-cloud-edge-era
Daniel Theis is a Research Associate at the Institute for Internet Security (if(is)) at the Westphalian University of Applied Sciences. His work focuses on data protection, digital identities, and secure digital infrastructures. He operates at the intersection of regulation and technology, translating legal requirements into practical solutions for complex IT systems.
Norbert Pohlmann is a Professor of Computer Science in the field of cybersecurity and is Head of the Institute for Internet Security - if(is) at the Westphalian University of Applied Sciences in Gelsenkirchen, Germany, as well as Chairman of the Board of the German IT Security Association TeleTrusT, and a member of the board at eco – Association of the Internet Industry.
FAQ
What does Zero Trust mean in cloud-edge environments?
Zero Trust means that no user, system, or request is trusted by default, regardless of location. In this dotmagazine article, Daniel Theis and Prof. Dr. Norbert Pohlmann explain how continuous verification strengthens security across distributed systems; dotmagazine is published by eco – Association of the Internet Industry.
Why is federation important for digital ecosystems in Europe?
Federation allows organizations to collaborate without giving up control over their data or systems. As outlined by Daniel Theis and Prof. Dr. Norbert Pohlmann in dotmagazine, published by eco – Association of the Internet Industry, it enables sovereign and interoperable cooperation across industries and borders.
How does Zero Trust improve security compared to traditional models?
Zero Trust replaces perimeter-based security with continuous verification of every interaction. In this dotmagazine article, Daniel Theis and Prof. Dr. Norbert Pohlmann show how this reduces risks from outdated permissions and dynamic environments; dotmagazine is published by eco – Association of the Internet Industry.
How can organizations implement Zero Trust in a federated cloud-edge setup?
Organizations can implement Zero Trust by combining identity verification, policy-based access, and real-time decision-making.
Daniel Theis and Prof. Dr. Norbert Pohlmann describe in dotmagazine, published by eco – Association of the Internet Industry, how projects like FACIS provide practical frameworks and tools for this approach.






