The Dangers of DDoS Overconfidence
Chris Townsley, EMEA Director at CDNetworks, discusses the rising threat of DDoS attacks, and the misplaced confidence of European businesses in their ability to overcome cyber attacks.

© BeeBright | istockphoto.com
DDoS attacks are growing in both number and size, and more and more often we are seeing their effects seizing the headlines. Take the Mirai botnet attack that targeted Dyn in October 2016 as an example – this prolific attack caused major service providers like Twitter, Amazon, and the BBC to be undermined, and is a perfect example of how cyber criminals are taking advantage of the growing number of connected devices to carry out cyber attacks en masse. If you combine this with the overall growth in cyber criminal sophistication (take the recent news of the Reaper botnet, which is said to have the potential to be even bigger than the Mirai botnet of 2016), the threat of DDoS quickly becomes a worrying concern to enterprises across all industries.
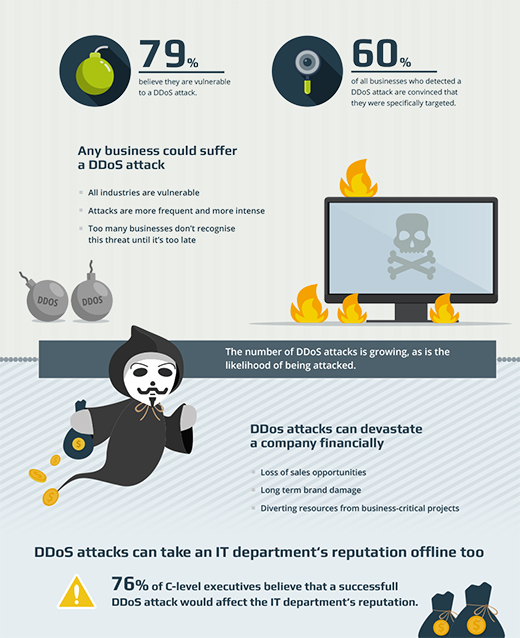
But despite warnings in the media and across the industry as a whole, many businesses believe ‘it will never happen to me’. In fact, businesses are confident in their preparedness to withstand a DDoS attack. But reality paints a very different picture – and businesses’ overconfidence in their DDoS mitigation could be putting them in great danger.
The DDoS attack landscape
According to data from CDNetworks, the number of DDoS attacks is growing, as is the likelihood of being attacked. In 2014, the number of DDoS attacks grew by 29% year on year, mostly targeted at the online gaming industry. Yet in 2015, attacks grew by an astounding 200%, aimed not only at the online gaming industry, but at public sector bodies and financial services too.
But attacks aren’t just growing in volume – they’re also growing in size. While the largest detected attack in the first half of 2015 was 21Gbps, in 2016, the largest attack was almost three times the size, at 58.8 Gbps.

Source: CDNetworks
With DDoS attacks becoming a bigger threat to businesses than ever before, CDNetworks investigated the preparedness, investment, and confidence of more than 300 businesses across the UK and DACH. While the good news (or at least, better news) is that 64% of businesses are set to increase their investment in DDoS mitigation in the next 12 months, the danger is that this will simply not be enough.
Misplaced overconfidence
The combination of widespread, recent, and growing investment in DDoS mitigation has led to overwhelming confidence amongst European businesses. 83% of respondents are confident, or very confident, in both their current DDoS mitigation arrangements and with how resilient they would be in two years’ time. And whilst 79% rate the likelihood of their infrastructure being attacked as between likely and almost certain, many believe they aren’t at risk of suffering the same fate as the likes of Twitter, Amazon, and the BBC.
But while the majority of businesses are confident concerning their preparedness, there is an underlying doubt from a minority of businesses, who harbor doubts about their preparedness. In fact, 44% of the respondents believe they are currently under-investing in DDoS mitigation.
Overconfidence or complacency?
While the recent high-profile DDoS attacks seem to have motivated businesses to invest in DDoS mitigation technologies, when we look at the number of attacks that have taken place, this confidence is misplaced. When asked about the frequency of DDoS attacks, 86% confirmed they had suffered a DDoS attack in the last 12 months.
But if confidence turns out to be complacency, the number of attacks is immaterial – it’s the number of successful attacks that is important. And despite how much money companies are investing and how confident they are in their technology, more than half of respondents (54%) have suffered at least one successful attack in the past year.
Which means this is more than simply a contrast between preparedness versus reality. The complacency of businesses is also echoed in how businesses believe DDoS will impact them. In short, until you have experienced a successful attack, you cannot really appreciate the damage it can do to your business.
Source: CDNetworks
While the administrative level is largely oblivious to how their reputation may be affected by failing to protect their business from attack, the C-suite cannot deny it would impact their view of the IT team, and were in fact the most likely to rate the impact as catastrophic. Understandably, the heads of the IT department felt the damage most keenly, being most convinced that their department’s reputation would suffer some or serious impact. IT heads therefore need to bear in mind that DDoS attacks are not only commercially damaging, but they will also affect their own prospects.
The answer for enterprises
The good news is, enterprises can take steps to ensure their DDoS mitigation is not under-provisioned. The first thing businesses need to do is test the severity of the problem. Performing a vulnerability test will identify where the gaps lie in systems and network defenses. This will entail an extensive review of their network’s strengths and weaknesses, and whether the DDoS mitigation tools in place are fit for purpose. This testing stage will then show where vulnerabilities lie, and highlight the services and technology needed to ensure businesses are protected.
Businesses also need to ensure they prepare for the worst. The lucky few that have not yet fallen victim to a DDoS attack underestimate their severity – and regardless of their confidence, businesses’ continuity needs to be a key part of DDoS planning. DDoS attacks can have catastrophic financial, legal, regulatory, and brand reputation effects.
Aside from the technical requirements of duplicating information and ensuring that recovery time objectives and recovery point objectives match business needs, there are also multiple procedural requirements. Identifying the crisis team and any security partners immediately, as well as having a communications plan in place, will ensure partners, employees, customers, and the media are kept informed if an attack takes place.
Finally, with the sophistication in cyber criminal activity rising, some DDoS attacks may come with a ransom demand. But paying cyber criminals is not recommended. Instead, businesses should consider having insurance policies in place. There will be some instances where cyber criminals win, and having insurance against data breaches and other types of attack will help to overcome some of the damage.
The DDoS arms race
‘It will never happen to me’ is a phrase often heard regarding personal health, home security, and driving safety, but it shouldn’t be a mindset taken towards cyber security. While European businesses are taking note and investing more in DDoS mitigation per year, this investment is not having the right effects – it’s leading to dangerous overconfidence.
Businesses need to ensure they aren’t taking the threat of DDoS lightly – the effects can be devastating if cyber criminals do in fact win. Without concerted new efforts, including fundamental changes in mindsets and more targeted technology investment, falling victim to a DDoS attack will be a matter of when, not if, for European businesses.

Source: CDNetworks
Chris Townsley is EMEA Director at CDNetworks, a global content delivery provider with fully integrated cloud security solution for an almost instant delivery of web content, even in hard-to-reach geographies such as China, South East Asia, and Russia.
Chris has been in the CDN industry for the past 10 years and has over 25 years of international experience. Having worked across a large number of industries and companies, Chris truly understands the challenges faced by companies looking to expand their online presence beyond domestic borders.
Please note: The opinions expressed in Industry Insights published by dotmagazine are the author’s own and do not reflect the view of the publisher, eco – Association of the Internet Industry.







