Sorting the Wheat from the Chaff - The Attention Value of Emails in an Ever-Increasing Stream of Messages
Willem Voogt from Aangetekend B.V. draws the comparison between attention value in physical and electronic mail, and looks at the influence of the eIDAS Regulation and the GDPR on email reliability.

© higyou | istockphoto.com
In a steadily increasing stream of received digital messages, reliability is a key word in terms of securing the reader’s attention: what is up for scrutiny is the identity of the sender and the recipient, the intent of the message, and the fact that the message is not changed during or after the shipment. The eIDAS-Regulation for Electronic Registered Delivery Service (ERDS) plays a pivotal role in ensuring such reliability, with the GDPR also weighing in increasing the reliability of emails. This paper makes a link between the terms of the eIDAS-Regulation for Electronic Registered Delivery Service (ERDS) and the attention value of emails. Throughout the paper, a comparison is drawn with the personal sorting of physical post as it occurred in times past.
In times when the postman often delivered the mail twice and at least once a day, and the use of the Internet was still reserved for an individual scientist or hobbyist, it was very easy to sort through a pile of mail. Based on the recipient’s own insight and experience – the envelope’s logo or typography, the paper used, the thickness of the mail item, and, having opened the mail, the texts and possibly the manuscript were simple means to quickly sort the important pieces.
With the current ongoing stream of emails and other digital messages, it is considerably more difficult to extract the relevant documents and to assign different priorities to them. We are constantly trying to transfer the old characteristics of physical mail to the digital version, but that turns out to be very difficult, if not impossible. In addition, the recipient can increasingly be wrongfooted by a strong increase in phishing and – even worse – spear phishing mails. In short: in the communication process between sender and receiver, changes must be made to achieve the desired effect.
This gives rise to the following question:
How can the correct message with the correct priority be delivered to the correct recipient and in the shortest possible time so that the correct (read: desired) action can take place?
In other words: how can the attention value of an email be made in such a way that the recipient can make an optimal selection of important, less important, unimportant, and SPAM messages – not to mention harmful malware messages with viruses, spyware, worms, trojans, rootkits, and so on.
The issue is perhaps even more difficult because cross-border email traffic is also more complex due to the sender's email address not necessarily being directly identifiable.
What is the scope of the issue?
Due to a number of autonomous effects, the problem is becoming more and more complex, which is partly caused by:
- The explosive increase in the number of mails sent and received per day;
- The strong increase in the number of Internet users worldwide;
- Digitalization of companies;
- The sharp increase in the number of (spear-) phishing emails;
- The professionalization of the phishing emails;
- A continuing large volume of spam messages;
- Increase in cross-border trade with associated email communication.
Since the first email was sent in 1971, email dispatch has now increased to an estimated volume of between 240 and 280 billion emails per day (see Fig. 1). Or to put it in more concrete terms: an average employee who uses Internet for his or her office work receives an average of 121 per day! Some are almost literally buried under the constant stream of emails. The hypothesis that email is being supplanted by social media (WhatsApp, Twitter, et cetera) is therefore not being borne out in email’s ever-increasing growth. (A small step aside: Things are looking up somewhat when it comes to spam messages: due to modified legislation and improved filtering techniques, the amount of spam is decreasing in relative terms.)
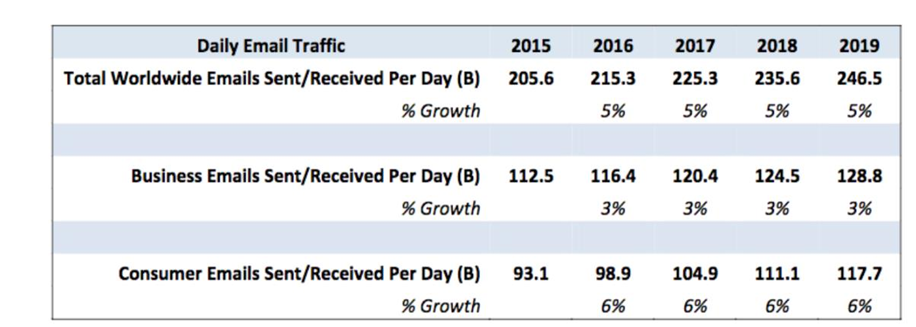
Daily Email Traffic (source: www.campaignmonitor.com)
All in all, this deluge of email messages tries to convey certain forms of positive – and unfortunately often negative – values to the recipient. Here we look at how to strengthen the attention value of emails and, in so doing, at how to avoid negative values.
Because ultimately, it is becoming increasingly important to separate the chaff from the wheat.
Logistics and the cognitive issue
The large amount of emails often presents a logistical challenge, which is comparable to, for example, the storage of things in and around the house: what do we store and how do we store it? Can we ever find it again if it turns out to be important? If we apply this thinking specifically to emails: Which folder structure do we use? Who can view or change or delete something?
On top of this comes the cognitive issue: it is difficult to keep track of the content of all messages, especially when it comes to an evolving issue in which several parties give their opinion by email simultaneously or promptly in a series of mails. This gives rise to what effectively is a “logistical issue in the head”.
Conversion rate
The term conversion rate is certainly not reserved for websites: with B2B and B2C email traffic it is an ultimate goal to score a high rate. In that respect, the so-called “my environments” are disastrous for attention value and therefore conversion: here, too, a comparison can be made with physical post. While someone regularly looks in the mailbox to see if there is mail, this is certainly not done in the “my environment” mailboxes without signaling. Despite all the efforts of governments, the average citizen does not always look at tax assessments and fines in the mailbox reserved for him or her.
Other “my environments” from the business world also do not seem to be a success. For most receivers, there are too many and then each – if it is used correctly – has its own password. And even if a signaling announcement is sent, the opening of the box is forgotten.
New developments to assist the recipient of emails
To accommodate the user somewhat in managing the daily flow of messages, more and more powerful and intuitive user interfaces, interfaces with other applications, spam filters, and other tools for managing, organizing, archiving, and searching for messages are emerging. For example, Basecamp and Superhuman profile themselves as important assistants.
But the real personal digital assistant – which checks the email in advance (!) for reliability, relevance, content, link with other messages and agenda items, level of priority, etc. has yet to be developed.
Reliability
The most important aspect in current email traffic is the reliability of the message:
- What is the identity of the sender?
- Is this the true identity and how certain/secure is that?
- What is the true intention of the sender of the message?
- Have changes been made to the message itself during the shipment?
In fact, these are questions that are very relevant in the daily use of email, which are often neglected in the current deluge of emails.
The legal security requirements of the email
Especially in trade, legal certainty of the use of email is decisive for efficient business processes, also across borders. Now, there has been a European Directive since 2009 in which the countries have to indicate via a legal provision that an email has a written status, provided that a number of requirements are met, namely:
- Email must be consultable for parties;
- Authenticity of the content must be guaranteed;
- The moment of creation must have been established;
- Identity of the parties must be sufficiently established.
Back to the physical post again: the remarkable thing is that an ordinary physical mail item does not meet any of these requirements, whereas a registered physical mail item only meets point 3, namely establishing the moment of creation (read: delivery). Incidentally, with the first two requirements, consider the situation that the sender of such a registered item sends a blank sheet and then claims that he or she has indeed delivered an important item.
So, if something goes over the digital road, the requirements become much higher than in a physical process. In the meantime, jurisprudence has arisen – at least in the Netherlands – in which the court has confirmed this in a ruling.
Obviously, a distinction must be made here between the use of emails in a harmony or conflict model. In the event of a conflict between the parties, for example, disagreement in the purchase of a product or disputes in labor law, testing against the above-mentioned requirements can be important.
The requirements mentioned above are also impossible in a standard mailing process, because the content of the mail and/or attachments can be adjusted unnoticed. Even if you send a read or receipt confirmation, if the recipient refuses to send the confirmation, the mail is still in his or her possession but you can never prove that he or she has received this mail.
At Aangetekend B.V., a Dutch firm which provides the Registered Email service in various countries in Europe, we now have the necessary experience in taking care of emails that have already fully complied with the European Directive from 2009 and also with the eIDAS-Regulation, which came into force from 2016 onwards in the EU.
The influence of the eIDAS Regulation on reliability
With the entry into force of Regulation (EU) No 910/2014, or the so called eIDAS-Regulation, major stumbling blocks in (cross-border) digital trade have been removed. As the regulation states, its aim is “enhance trust in electronic transactions in the internal market by providing a common foundation for secure electronic interaction between citizens, businesses and public authorities, thereby increasing the effectiveness of public and private online services, electronic business and electronic commerce in the Union.” [1]
The eIDAS-Regulation is about electronic identification means and so-called trust services. Among these services, the Electronic Registered Delivery Service (ERDS) includes electronic signatures, seals, time stamps, and documents.
On the basis of strict conditions with which the services must comply, courts or other bodies in charge of legal proceedings cannot discard them as evidence simply because they are electronic, but have to assess these electronic tools in the same way as they would for their paper equivalent. These conditions are described for ERDS in Articles 43 and 44 of the Regulation. Article 43.1 concerns the integrity of the content of the mail by an identified sender and the times at which the various actions take place (send, receive, and open). Articles 43.2 and 44 goes a number of steps further in terms of reliability: this also concerns the accurate identification of both sender and receiver.
The GDPR also affects the reliability of e-traffic
Under the operation of the General Data Protection Regulation (GDPR), which has been in force in all EU countries since April 2018, organizations must be able to provide insight into how personal data are processed in their email systems. Certainly, in view of the heavy sanctions that may follow violations of the strict rules, organizations have become much more careful in sending emails.
Attention value
For the recipient, it is pleasing in the context of sorting and prioritizing emails if their reliability is already guaranteed by either Article 43 or Article 44 of the eIDAS Regulation. This effect seems to be catching on: Many companies already have their physical postal services replaced by emails that comply with one of these articles, not only to save considerably on the handling costs, but also to obtain a higher conversion.
And the recipient is helped by the fact that he or she is better able to quickly dispose of emails with lower priority, such as advertising brochures, magazines, and other minor items, so that – to return to the initial question of this paper – the right attention can be directed to the right pieces. For the recipient, every new assurance of reliability means that a received mail also contains a more relevant message.
In addition, there are, of course, additional possibilities to increase attention values, for example by using short personalized subject rules.
Separating the wheat from the chaff
For the sender, but above all for the recipient of digital messages, it is important that the right message is delivered at the right time and with the right intention. The reliability of the sender, but also of the receiver themself, and of the content of the message – these are of the utmost importance.
Emails that complies with Article 43.1 or in some cases Articles 43.2 and 44 of the eIDAS Regulation is an important tool for both parties.
In this way, in the current multitude of emails, some order and priority can be obtained.
Please note: The opinions expressed in Industry Insights published by dotmagazine are the author’s own and do not reflect the view of the publisher, eco – Association of the Internet Industry.





