The Most Dangerous DDoS Attacks of our Time
Dmitry Samoshkin from G-Core Labs advises on what you need to know about DDoS attacks and how to prepare for them.

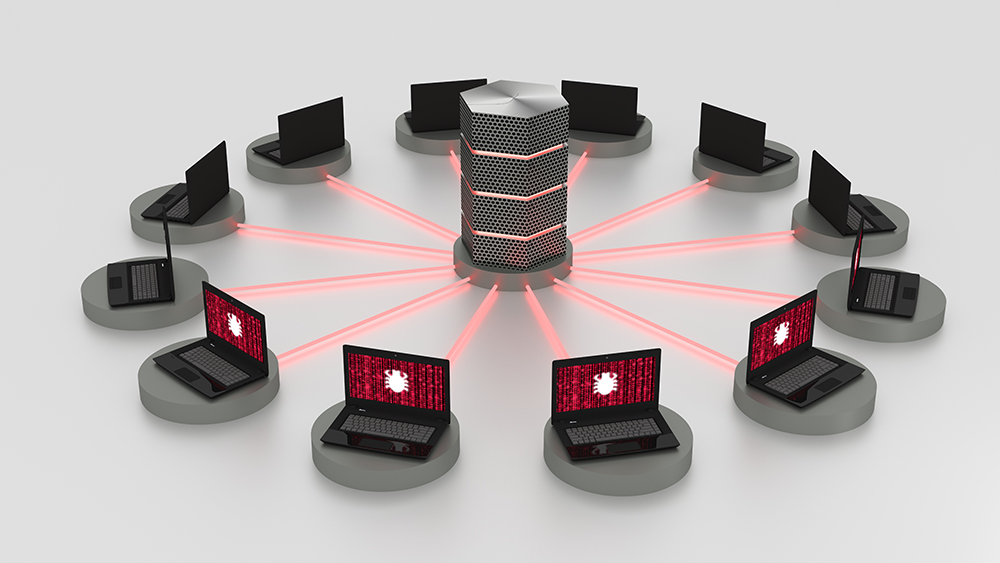
© BeeBright | istockphoto.com
As projects and organizations grow, they acquire new resources and, accordingly, they face new threats. Sometimes even small businesses become victims of cybercrime.
The reasons for attacking digital resources can vary from hunting for valuable data and access, to intentionally damaging an organization’s reputation and finances. In any case, security should be the top priority.
Over the last few years, cloud infrastructure, and especially the public cloud, has become very popular. Thousands of companies worldwide, from small businesses to massive giants, rely on cloud services.
Cyber threats can harm any online business if appropriate security measures aren’t in place.
Types of DDoS attacks
DDoS attacks (Distributed Denial of Service) are one of the most widespread cyber threats. Their goal is to literally deny service.
Such attacks disrupt the functioning of servers, websites, and web services by flooding them with an excessive number of requests. Resources that aren’t designed for high loads then stop working, thus becoming unavailable to users. Also, DDoS attacks exploit vulnerabilities at the network protocol and application layers.
The term ‘distributed’, when applied to this type of attack, means that perpetrators covertly use entire networks of infected devices – botnets – as sources of attacks. Device owners often have no clue that attacks are being performed from their computers and IP addresses. Devices within the Internet of Things (IoT) are especially suitable for such purposes because the number of them continues to grow while the protection they have remains quite weak.
Even though almost half of DDoS attacks are of a mixed nature, three main categories can be named.
Volumetric attacks
High volume attacks (i.e. flooding). This is the most widespread type. Perpetrators send a large number of requests to the server, and the resulting traffic blocks network bandwidth capacity.
The volume of such attacks can reach several terabits per second. As a result, unprepared infrastructures crash and stop processing requests.
Protocol attacks
These attacks exploit vulnerabilities of such network protocols as TCP, UDP, and ICMP (Layers 3 and 4 of the OSI model). In this case, the purpose is to overload network capacity not with a giant amount of traffic but with pinpoint actions that exploit network defects.
Application attacks
These are application layer attacks (Layer 7 of the OSI model). They are aimed at web servers and applications, such as a website’s CMS. The main purpose is to knock the web resource out of service. This can be done, in particular, by overloading the CPU or RAM.
This can be achieved with an external HTTP request. In response, the system starts processing a large number of internal requests it’s not designed for.
The most dangerous DDoS attacks of our time
Due to the high effectiveness of some attacks, they are particularly popular among perpetrators. The most serious incidents of our time are related to special types of DDoS attacks.
DNS Reflected Amplification
This subtype of volumetric attacks is a combination of two malicious factors. First, the attacker simulates a request from the targeted server by putting its IP address into the request, ultimately using a public DNS server as a “reflector.” The DNS server receives the request indicating the targeted server and returns a response to it, thus “reflecting” the request.
A lot of data, not just the IP address of the domain, can be requested, which means the response of the DNS server can become many times larger. Finally, traffic can be maximized by querying through a botnet. Thus, it is highly likely that the bandwidth of the targeted server will be overloaded.
The attack against GitHub. The most famous use of DNS Reflected Amplification was the attack on GitHub in February 2018, which is the largest known DDoS attack. It came from thousands of different autonomous systems and tens of thousands of unique endpoints. The attack reached 126.9 million packets per second at peak times. The traffic flow reached 1.35 Tbps, and the gain ratio (amplification ratio) reached 51,000.
Generated UDP Flood
Generated UDP Flood combines the generation of excess traffic and elements of protocol-layer attacks.
The attack sends UDP packets from fake IP addresses to a targeted IP address and server port. With a correctly-selected packet parameter and intensity of sending, it’s possible to simulate legitimate traffic. Identifying junk requests then becomes extremely difficult.
Such an attack was carried out against the Albion Online MMORPG server. As a solution to eliminate the threat, a G-Core Labs software package combining various methods was selected:
Rate Limiting—limitation on traffic
Regexp Filtering—filtering packets that coincide with regexp in payload
Whitelisting—adding authorized player IP addresses to a whitelist
Blacklisting—adding unauthorized player IP addresses to a blacklist
IP Geolocation Filter—blocking IP addresses based on geolocation
G-Core Labs Challenge Response (CR)—a unique protocol that is integrated on the client’s side and that allows IP address validation
There are other types of DDoS attack as well, such as the HTTP GET/POST Flood, which, according to open sources, was used to attack several large Russian banks in November 2016. Hit-and-run, a subtype of volumetric attacks, is mainly used to target online game servers and service providers. In addition, some of the largest companies in the world, including Amazon, SoftLayer (IBM), and Korea Telecom have become targets of SYN Flood and similar types of attacks.
One serious incident was the disabling of the Eurobet Italia SRL sports betting website in October 2019. Later that month, several financial and telecommunication companies in Italy, South Korea, and Turkey fell victim to TCP SYN-ACK Reflection. Finally, Slowloris (or session attack) aims to “exhaust” the targeted server. The perpetrator opens many connections and keeps each one open for as long as possible until timeout occurs. This type of attack became widely known during the Iran presidential election when attackers attempted to disable government websites.
How to set up reliable protection: 3 main steps
Cybersecurity is a narrow competency that can hardly be covered as easily as HR or accounting, no matter how advanced the company is. It’s important to ensure that your service and infrastructure providers are deeply immersed in cybersecurity issues and have established themselves as true professionals.
The 3 main steps companies need to take for reliable protection are:
- Use a tried-and-tested solution for continuous DDoS protection.
- Develop an action plan in case of an attack.
- Regularly run system health checks and eliminate application vulnerabilities.
A proven solution for continuous DDoS protection
When we consider cloud infrastructure security, special attention is required.
A server is one of the foundations for any web service, application, or site. If an attack leads to a loss of user access to resources, the consequences can be disastrous. There are financial and reputational risks, the potential compromising of confidential information, the destruction of valuable resources, and legal risks.
To keep your assets safe, it’s important to use proven online protection.
Protection should include the following elements:
- Tools for continuous traffic monitoring and detection of suspicious activity
- Adding IP addresses to blacklists and whitelists
- Threat notification system
- Attack neutralizing system
It’s especially important not to block user traffic along with malicious traffic when eliminating the threat.
A good example of effective fine tuning is G-Core Labs’ DDoS Protection Service. This service is useful for any online business: media resources, game developers and publishers, telecom companies, insurance business, banks, and online stores.
Intelligent traffic filtering based on the analysis of statistical, signature, technical, and behavioral factors makes it possible to block even single malicious requests without affecting ordinary users.
An action plan in case of an attack
A response plan aims to limit the damage caused by a DDoS attack. It’s a clear sequence of actions and measures to be taken immediately as soon as a threat occurs.
A detailed action plan should include the following:
- Complete list of resources under attack
- Localization of the threat and prevention of its spread
- Notifying stakeholders about the incident
- Identifying the nature of the threat, detecting digital traces
- Identifying the methods and means of the attack
- Full scan of the IT infrastructure, damage assessment
- Control of outgoing traffic and data leakage prevention
- Threat elimination
- Preparation to counter similar attacks in the future
Regular system health checks and elimination of application vulnerabilities
To prevent a surprise DDoS attack and keep damage to a minimum, the protection mechanisms should be constantly improved. This rule applies not only to the tools designed to repel attacks, but also to the protected infrastructure and application.
Here’s a list of potential threats:
- Authentication stage vulnerabilities
- Malicious code insertions
- Cross-site scripting
- Encryption vulnerabilities
- Logical errors, imperfect data structure
Scanning systems for vulnerabilities and constantly updating application code will help keep company resources resilient to most known cyber threats.
15+ years experience of working in the information technology and services industry. As VP Products at G-Core Labs, Dmitry Samoshkin is responsible for such product and service development as CDN, Storage, Cloud, Media & Security and Software Development. Dmitry is a professional motorsport driver participating in international Drift Championships and competitions.
Please note: The opinions expressed in Industry Insights published by dotmagazine are the author’s own and do not reflect the view of the publisher, eco – Association of the Internet Industry.